31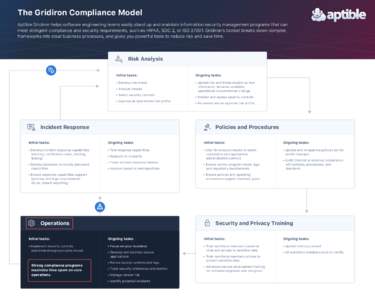 | Add to Reading ListSource URL: www.aptible.com- Date: 2018-03-21 14:07:12
|
|---|
32 | Add to Reading ListSource URL: www.targetedjobfairs.com- Date: 2017-05-16 17:41:34
|
|---|
33 | Add to Reading ListSource URL: www.first.org- Date: 2017-08-08 15:42:43
|
|---|
34 | Add to Reading ListSource URL: arxiv.org- Date: 2017-07-20 21:01:01
|
|---|
35 | Add to Reading ListSource URL: tuprints.ulb.tu-darmstadt.de- Date: 2011-04-18 10:27:51
|
|---|
36 | Add to Reading ListSource URL: www.patrickmcdaniel.org- Date: 2016-11-26 07:36:40
|
|---|
37 | Add to Reading ListSource URL: ceur-ws.org- Date: 2010-06-24 06:51:12
|
|---|
38 | Add to Reading ListSource URL: www.cis.syr.edu- Date: 2004-09-16 15:50:23
|
|---|
39 | Add to Reading ListSource URL: dl.dropboxusercontent.com |
|---|
40 | Add to Reading ListSource URL: media.blackhat.com- Date: 2013-07-31 04:48:48
|
|---|